COMPUTER SECURITY, HOW BAD IS IT?
(A special report by volunteers of The Open Records Project)
August 3, 2021
COMPUTER SECURITY, HOW BAD IS IT?
(A special report by volunteers of The Open Records Project)
August 3, 2021
|
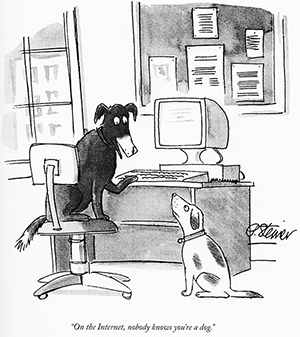
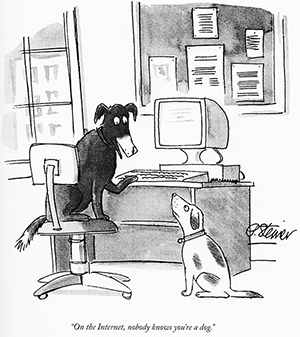
"On the Internet nobody knows you're a dog."* Similarly nobody knows you're a cyber-criminal. Computers were one of man's greatest inventions. Then the Internet brought computer power to millions, some of whom were very bad people. This paper will analyze both.
EXECUTIVE SUMMARY Internet connectivity increases the risk of intrusion, but any computer that allows external input devices including USB drives, DVD/CD readers, scanners, printers, or wireless connectivity of any kind must be considered similarly at risk.
The risks derive from four primary elements:
TABLE OF CONTENTS
HOW THE INTERNET WORKS AND DOESN'T WORK
Of course many people are deluged with junk phone calls that show an "originating" phone number and sometimes a name. The phone spammers know how to fake the "originating" number so you will answer the phone instead of ignoring it. Internet hackers do the same thing with IP numbers. The hacker can make the IP number be anything, the IP of a trusted compatriot or just a random number. Sometimes the hacker will use a compromised computer to relay a message to a destination thereby showing the IP of the compromised computer. If an IRS computer has been compromised, the hacker can bounce the message off the computer and make it appear to originate with the IRS. The ease of hacking IP addresses makes identifying cyber-criminals very difficult.
THE INTEL/AMD ATTACK SURFACE
The techniques include:
The results do yield performance improvements but entail massively complex logic to implement. As with complexity in operating systems, complexity in logic leads to oversights and security holes.
These are five of the more important security vulnerabilities found in INTEL/AMD computer architectures:
THE OPERATING SYSTEM ATTACK SURFACE Microsoft Windows 10 is installed on over a billion devices worldwide making it the largest target for hackers.
The most recent and most severe ones include:
Computer programs and particularly operating systems are highly complex. Windows 10 consists of over 50 million lines of program. No single individual can comprehend all the operations. Legacy programs like Windows contain millions of lines written decades ago that are just copied into each successive revision. The individuals who wrote that code and understood how it worked are long gone. As a result attempts to patch vulnerabilities often both break functionality as well as introduce new vulnerabilities. Microsoft thought it patched the printnightmare hole but the patch had its own bug. The history of Microsoft's lengthy and ongoing security breaches is compelling evidence that NO MICROSOFT SOFTWARE should ever be considered secure and that NO MICROSOFT SOFTWARE should ever be used for mission critical applications.
SOCIAL ENGINEERING The paper Principle of Persuation specifies five elements of persuasion:
1.Authority: Use of an authoritative name, e.g., a company CEO In other words, don't click on an EMERGENCY link emailed from your boss criticizing your recent work. Also, don't click on "photos" of Kim Kardashian. The clicked link can include everything from a scripted WORD document to a corrupted image file to an innocent looking Javascript block. All can contain malware which can render your computer available for intrusion.
Flash drives actually contain a small embedded computer that handles error correction and reliability algorithms. Sophisticated perpetrators can re-program this embedded computer to change the drive's contents. The Internet has re-programming instructions simple enough to be performed by a high school student. Here is a flash re-programming tutorial in Russian. Several devastating intrusions were executing using USB flash drives including:
STUXNET which destroyed thousands of Iranian nuclear centrifuges,
PERPETRATORS AND BUSINESS MODELS Current perpetrators appear to be a mixture of professional cyber-criminals seeking monetary gain and state actors seeking political advantage. In some cases it's possible that state actors are contracting with criminals who may possess more sophisticated intrusion skills. The money to be made is immense. Determining the identity of hacking organizations is difficult since on the Internet, "Nobody knows you're a dog." "Organization" names are created and destroyed in an instant. Some groups use different names at different times. Some are strickly mercenary and some are completely state owned.
A few examples with guesses as to their countries:
There are actually cyber-criminal TRADE SHOWS
TWO COMMON MEANS OF DESTRUCTION Paying ransom has at least three downsides beyond the loss of money. First, the perpetrators sometimes take the money and don't release the decryption keys. Second, even if the decryption keys are delivered and files are recovered, there is no guarantee that the original vulnerability will not be attacked again. Con artists often repeatedly hit soft targets who have shown willingness to pay. Third, the perpetrator may run an extortion based on the data revealed in the ransom attack.
NEXT-GEN EXTORTIONWARE What is the value of extorting a president's son? The beauty of Next-Gen Extortionware is the near impossibility of prosecuting the crime. Kidnappers and extortionists get caught when physical people try to collect physical ransom. In cyberspace neither the money nor the people are real. They are bits and bytes representing Bitcoin or Ethereum and IP addresses to temporary email addresses at Internet cafes in Bangladesh.
ELECTIONS
University Grade Hack
Due to the ease of hacking election computers NO COMPUTER or computer containing device should be used to mark or count election ballots. All ballot marking and ballot counting should be done manually with paper ballots. Computers should only be used for voter registration, and then only with great care.
IMPLICATIONS The ORP is not the only organization making that prediction. Gartner Predicts Hacked Computers Will Start Killing People By 2025. Gartner is a $4.5 billion IT consulting shop with 15,000 employees worldwide. Their press release is clearly designed to drum up business, but they do have a point.
UPDATE: In February 2021, Microsoft President Brad Smith said that it was "the largest and most sophisticated attack the world has ever seen". On the August 3, 2021 Q2 2021 Earnings Call SolarWinds President and Chief Executive Officer said, "It is an unfortunate fact that no company regardless of its size, competency, and resources seemed immune to cyber attacks as evidenced by the recent high-profile breaches."
ASYMMETRICAL WARFARE, PROXY WARRIORS
- They can negate hundred billion dollar military investments of much larger opponents. The Berkman Klein Center at Harvard has proposed modifications to international law to mitigate the threat. The proposed modifications could replicate successes of the Kellog Briand Pact and the Washington Naval Treaty.
GOVERNMENT RESPONSE The Nation Security Agency motto is "Defending our Nation. Securing the Future." It is an intelligence agency of the US Department of Defense. With a classified budget and staffing believed to be $10.8 billion and 30,000-40,000 employees. it is the premier national cyber-security facility. Like most intelligence agencies the NSA is controversial as it attempts to thread the needle between citizen security and national security. The agency appears to have prioritized national security over citizen security and offensive capabilities over defense. As a result it left both itself and US citizens with a less than robust protection from computer intrusions. NSA runs the Office of Tailored Access Operations (TAO) to collect and develop tools to hack into any computer, router, firewall, or other electronic device. The Equation Group is a collection of hackers and hacking tools believed to be associated with TAO. As such they have access to the massive resource of the NSA. In 2016 a hacker group called The Shadow Brokers penetrated the Equation Group computers and copied all the hacking tools. These tools were released into the wild over the next several months. One of the NSA tools was co-opted by the North Koreans to launch the Worldwide WannaCry ransomware attack infecting 230,000 computers in 150 countries. Estimated costs incurred due to the attack ran into the billions of dollars. It is very easy to blame the NSA for letting itself get hacked, having its hacking tools stolen, and having its stolen tools wreak havoc across 150 countries. However the NSA uses computers like the rest of the world. If you use a computer, no matter how sophisticated you are and how many billions you have for security, NO computer can be protected from intrusion, not even an NSA computer. The FBI also has a cyber-crimes division. Their primary activity seems to be posting MOST WANTED cyber-criminals. Most of the names posted appear to be foreign nationals of powers hostile to the United States. Furthermore there seems to be no list of CAPTURED CYBER-CRIMINALS. Tough guy Secretary of State, Anthony Blinken, decided to up the US game on July 24, 2021 bragging, "There's a new sheriff in town" for cyber-warfare. The laughter from cyber-criminals could be heard across two oceans.
The only thing worse that being laughed at is having a leader discuss getting into a "shooting war" over a cyber-breach.
POSSIBLE SOLUTIONS Furthermore to fight pirates you don't send billion dollar bureaucracies that can't keep their own secrets, or Harvard inspired ambassadors with treaties and pacts, or a private school educated "sheriff" who can't spell computer. You send computer-savy corsairs with Letters of Marque.
Instead of creating a international incident and killing hundreds or thousands in collateral damage, be sophisticated and nuanced but send a precise and pointed message:
- In winter turn off the heat to the cat-house favored by party elite when they are celebrating Stalin's Birthday.
If something more kinetic is called for, run a Politburo Supercar off a building during the May Day speech. The message should be crystal clear, If you mess with the US, we will turn your lights out. Have a nice day.
As always, if you know something say something, and say it to WHISTLEBLOWER@openrecords.org. * Peter Steiner's New Yorker cartoon https://upload.wikimedia.org/wikipedia/en/f/f8/Internet_dog.jpg
|